Wall Street is rushing to put traditional assets on blockchains. The headlines promise 24/7 liquidity, instant settlement, fractional ownership, and a tidal wave of institutional capital. Those marketing lines are seductive. But beneath them sits a compliance architecture that quietly flips the power dynamic: instead of crypto forcing financial incumbents to change, those incumbents are building rails that make crypto conform to their rules.
Table of Contents
- Where the momentum is coming from
- But read the fine print: adoption or control?
- BlackRock’s BUIDL fund: a case study
- The economic case—and who captures the value
- DeFi being permissioned: real-world examples
- When censorship is a business decision
- What this means for the original promise of crypto
- Practical guide for individuals and traders
- Where tokenization might be positive
- How to spot a Trojan horse
- Balancing engagement with preservation
- Conclusion
- What is ERC-3643 and why does it matter?
- Will tokenization automatically raise the price of base-layer tokens like ETH?
- Are permissioned tokens “crypto” or just regulated IOUs?
- What should retail holders do to protect optionality?
- Can institutional and permissionless models coexist?
- How can traders take advantage of RWA tokenization developments?
Where the momentum is coming from
The speed and scale of institutional tokenization is real. Consider a handful of data points:
- BlackRock, the world’s largest asset manager, has launched a tokenized fund designed to hold short-term US government paper as on-chain units.
- JPMorgan has processed over $1 trillion through its internal token settlement rails.
- Major banks and infrastructure firms are publishing optimistic market estimates predicting trillions of dollars in tokenized assets by 2030.
- The tokenized treasury market jumped by hundreds of percent in a single year—real growth, not just hype.
All of this has a straightforward logic: higher on-chain utility should increase demand for base-layer blockspace and therefore benefit tokens like ETH and other layer-1 assets. That is the simple bullish story many celebrate.
But read the fine print: adoption or control?
The key sentence often buried in investor letters is not about yield or viability; it’s about identity. Institutions make tokenizing regulated assets legal only if they can enforce identity verification and anti-money-laundering controls at the ledger level. That simple requirement transforms how tokenized assets behave.
How permissioned tokens are made to run on permissionless layers
The most widely adopted technical approach to this problem is a smart contract standard that layers identity checks into every transfer. One such standard enforces on-chain identity and whitelisting: every transfer first queries an identity registry, and if either the sender or the recipient is not approved, the transfer fails.
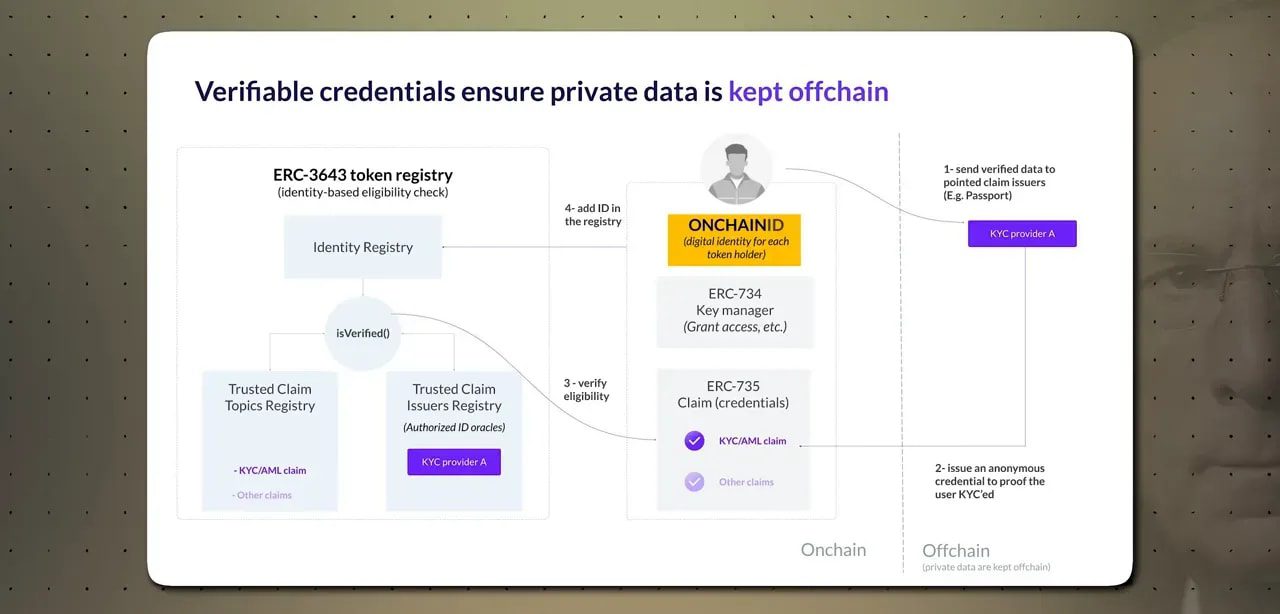
This is the opposite of the default crypto model. Standard ERC-20 tokens allow anyone to send or receive tokens; the token contract does not check who you are. The compliance-first standard reverses that: identity is a mandatory gate. Worse, the administrators of those registries are granted powers baked into the standard:
- Freeze individual addresses.
- Force transfers without a holder’s consent.
- Recover tokens from wallets whose private keys are lost.
These features are not incidental. They exist precisely so regulated institutions can satisfy securities, custody, and AML requirements. Companies building this architecture now power tens of billions of dollars in tokenized assets and have been integrated into major market infrastructure providers.
BlackRock’s BUIDL fund: a case study
The BlackRock product often cited as a watershed moment is a tokenized money market fund built to hold government bills and operate on a public smart contract platform. Look at the contract and you do not see pseudo-anonymity or open DeFi primitives. You see a built-in whitelist mapping approved investor wallet addresses.
The whitelist is managed by a regulated transfer agent and broker-dealer that runs KYC and AML onboarding. Minimums are set like institutional products: multi-million-dollar entry checks and large redemption minimums. In short, it is not retail DeFi wearing a suit. It is institutional finance deployed on public rails.
The product was later announced to be listed on a leading decentralized exchange. On paper that looks like a bridge between the old and the new. In practice the DEX is merely an execution layer: only whitelisted, verified addresses can hold the token. The listing proves one thing: open-source protocol code is being used to host markets that remain closed to anyone who hasn’t passed an off-chain compliance gate.
The economic case—and who captures the value
There is a real yield argument for putting treasuries and other short-term instruments on chain. When risk-free yields are higher, programmable collateral unlocks new possibilities for lending, derivatives, and automated risk management that simply did not make sense when yields were minimal.
But not all token plays capture the upside for token holders. Compare two different outcomes:
- Protocols that route actual RWA income back to token holders—for example, some platforms use RWA-derived fee revenue to buy and burn protocol tokens, directly creating economic value for holders.
- Infrastructure governance tokens—some tokens represent governance over platforms that service institutional clients. Those institutions often capture the fees, and governance tokens do not automatically entitle holders to revenue, leaving retail token holders sidelined while the platform grows.
The difference is the difference between being “in the room where it happens” versus being a spectator. If you are evaluating exposure to tokenized real-world assets, look carefully at where the revenue goes, who controls the whitelist, and whether token economics are aligned to distribute value.
DeFi being permissioned: real-world examples
The co-option of DeFi is not hypothetical. Several major protocols have already created permissioned versions or layers:
- A decentralized lending platform built a permissioned variant that required users to be whitelisted by a regulated custodian, which also held guardian rights to veto governance actions deemed compliance risks.
- Another major protocol announced a permissioned market for tokenized RWAs that uses an automated compliance engine to enforce KYC/AML rules across chains. The marketing slogan: permissioned collateral, permissionless liquidity—an elegant way to describe what is actually permissioned infrastructure using permissionless code.
- Cross-chain messaging infrastructure providers now offer compliance modules that screen assets as they move between chains. Firms participating in these systems include global banks and regulatory intelligence vendors that previously specialized in on-chain surveillance.
The practical effect is that the once-free movement of tokens across chains is being replaced in many cases by filtered movements: before the token lands in your wallet on Chain B, it has been screened against a compliance policy and the recipient’s whitelisted status.
When censorship is a business decision
The idea that a blockchain cannot censor transactions is a common misconception. Censorship can occur upstream—by block builders, validators, or relayers—who make commercial choices about what they will include in the blocks they propagate.
In a notable past episode, a large portion of blocks on a leading smart contract platform began excluding transactions tied to a sanctioned mixing service. At its peak, most blocks complied with the sanction by choosing not to include those transactions. This censorship did not require a protocol upgrade or a vote from the developer community; it required a handful of operators to adjust their risk calculus. That is centralization in practice, regardless of the theoretical decentralization of the protocol.
What this means for the original promise of crypto
Early crypto ideals were explicit: money outside of state control and applications that run without asking gatekeepers for permission. Those ideals were political and technical at once. The current institutional trajectory aims at a different end: make crypto convenient for regulated finance while preserving their ability to control participation and transaction flows.
That trend is not inherently evil. Institutional efficiency and better settlement systems can be useful. The issue is whether the tradeoff—efficiency in exchange for pervasive identity and reversal powers—is worth it for the ecosystem as a whole.
Practical guide for individuals and traders
If you hold crypto or are thinking about exposure to tokenized RWAs, here are practical considerations:
- Understand the token standard and permissions. Is the token permissionless or does it implement on-chain whitelist checks? Read the smart contract or rely on trusted analysis. If administrators can freeze or reverse transfers, treat the token as a regulated IOU rather than an uncensorable asset.
- Follow the money flows. Does the protocol route RWA-generated fee revenue back to token holders, or does revenue accrue to institutional clients and custodians? Tokens with direct revenue mechanisms are likelier to benefit retail holders.
- Keep custody in mind. Self-custody of permissionless assets still matters. Truly permissionless networks remain outside the scope of many current regulatory frameworks. If preserving optionality is important, custody decisions are central.
- Watch governance architecture. If a private company has guardian rights with veto power, the protocol cannot be considered permissionless in practice—even if the code is open-source.
- Stay informed on proposals and protocol-level changes. New proposals aim to make censorship harder on base layers. Supporting genuinely decentralized infrastructure matters if the goal is to preserve uncensorable money and applications.
For traders focused on short-term opportunities created by these institutional moves, having access to timely market signals can help. A service that delivers curated crypto trading signals—highlighting rapid shifts in RWA adoption, listings, and liquidity flows—can give a tactical edge when markets reprice on compliance or regulatory news.
Where tokenization might be positive
While the critique is sharp, there are constructive outcomes:
- Faster settlement and programmable collateral can reduce systemic risk in traditional markets.
- Tokenized assets could unlock new credit and liquidity products when properly designed.
- Some protocols are aligning token economics so that retail holders actually benefit from RWA revenue—these are the models worth supporting.
The core distinction is whether tokenization is used to extend financial inclusion and innovation or whether it becomes an exercise in controlled efficiency that simply transposes existing surveillance and gatekeeping into new technical forms.
How to spot a Trojan horse
Red flags to watch for when evaluating tokenized products:
- Mandatory KYC/whitelists enforced at the smart contract level.
- Administrative powers to freeze, reverse, or forcibly transfer tokens.
- No explicit mechanism for sharing RWA revenue with token holders.
- Governance roles assigned to regulated custodians with veto rights.
These are not accidental design quirks; they are features to meet regulatory requirements. The question is whether those features should become the norm across the broader ecosystem.
Balancing engagement with preservation
Tokenization is going to happen. The data already shows rapid institutional uptake. The strategic choice for the crypto community is whether to let institutional norms fully reshape the space or to preserve a thriving slice of genuinely permissionless infrastructure.
Four practical steps to balance both realities:
- Support protocols and proposals that limit censorship at the base layer.
- Prioritize self-custody and educate users on the difference between permissioned tokens and uncensorable assets.
- Back token economics that return RWA revenue to decentralized token holders rather than concentrating it with institutions.
- Use market intelligence—like curated trading signals—to understand how institutional moves translate into price action and liquidity flows across networks.
Conclusion
The push to tokenize trillions of dollars of traditional assets is a watershed moment. It will reshape markets, infrastructure, and how value moves on-chain. That could be beneficial—but it could also erode the foundational promises of crypto: privacy, permissionless access, and resistance to centralized control.
The choice is not only technical; it is political and economic. Institutional adoption can coexist with a robust permissionless layer—but only if the community is clear-eyed about tradeoffs and deliberate about which norms it allows to take root. Tokenization should not be an unquestioned victory lap. It should be an occasion to decide what type of ecosystem is being built.
What is ERC-3643 and why does it matter?
ERC-3643 is a token standard that integrates on-chain identity and whitelist checks into token transfers. It enforces KYC/AML controls by preventing transfers to or from unapproved wallet addresses and grants administrators powers like freezing addresses and executing forced transfers. It matters because it enables regulated assets to exist on public chains while preserving institutional compliance controls.
Will tokenization automatically raise the price of base-layer tokens like ETH?
Not automatically. Tokenization increases on-chain utility and could boost demand for blockspace, but the economic outcome depends on whether tokenized assets create genuine on-chain activity that benefits decentralized token holders. If institutional products are permissioned and revenue accrues to institutions, the price effect on base-layer tokens may be limited.
Are permissioned tokens “crypto” or just regulated IOUs?
Technically they are tokens, but functionally many behave like regulated IOUs. If a token requires whitelisting and administrators can reverse transfers, it operates more like a traditional custodial instrument with blockchain plumbing rather than an uncensorable asset.
What should retail holders do to protect optionality?
Prioritize self-custody for permissionless assets, scrutinize token economics for revenue-sharing mechanisms, avoid overexposure to tokens governed by custodial vetoes, and support protocol-level proposals that harden base-layer resistance to censorship.
Can institutional and permissionless models coexist?
Yes, coexistence is possible. The challenge is ensuring a meaningful permissionless layer remains. That requires advocacy, careful protocol design to limit centralized control, and community support for proposals that protect uncensorable transactions.
How can traders take advantage of RWA tokenization developments?
Traders can monitor listings, liquidity migrations, and compliance-driven events that create volatility. Using timely market intelligence and curated crypto trading signals helps capture short-term mispricings as institutional flows and regulatory news reprice assets across chains.